My company, Talia, provides hosted Voice-over-IP (VoIP) services to our customers. A typical use is a software-based PBX such as Asterisk on our virtual machine hosting cluster (or as the kids say, our “cloud”). We use the same for our own corporate PBX.
In the past month, we’ve experienced two fraudulent attacks costing a few hundred USD each. We have measures to detect and prevent such things, but that’s not what I want to talk about. I want to talk about how these attacks occurred.
Here are the relevant facts:
- One came from a staff extension in one of our offices to our corporate PBX. The other was from a customer’s extension to his hosted PBX.
- The extensions were different hardware – one was Cisco SPA502G, the other was D-Link ATA (analog telephone adaptor).
- The fraudulent traffic did not originate with the extension hardware. Rather, the SIP credentials were used to login from other locations and send calls.
- The extensions were left on public IP addresses with default passwords.
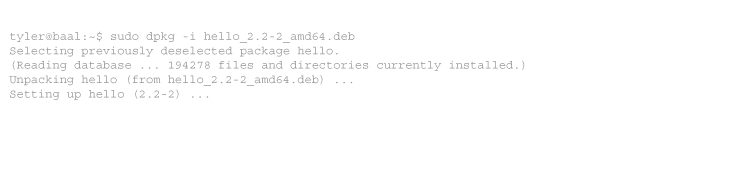
- It is possible to retrieve the SIP credentials from the web interface of the extension hardware. The password is obscured by “********”, but this is trivial to defeat.
Obviously, these were not configured by my staff, or someone would be scrubbing toilets right now.
In both cases, the fraud appeared within 24 hours of each other, and in one case, within 24 hours of the extension hardware being put online. With admittedly little data, the conclusion is nonetheless obvious:
VoIP fraud gangs have fully automated the process of identifying weakly-protected VoIP devices, scraping the SIP credentials, and using them to send calls as authenticated users.
As always, you should follow sane security guidelines.
- Always change the default password to a secure, preferably random value.
- Carefully guard any password which can cost you money. You are probably careful about your bank and credit card, but did you think about your mobile phone account? Your logins for services paid by direct debit?
- Set very long, strong, random SIP secrets. It wouldn’t have helped here, but you should do it anyway.
- Don’t put ANY VoIP device on a public IP, unless it is carefully firewalled.
- Only sign up for pre-pay voice services, and do not use automatic top-up. You should never lose more money than you have already paid in.
-
When we installed our PBX, which runs on Asterisk in the backend, I noticed random traffic after few hours of it’s install, and it filled my sip logs. I did the exact same steps you mentioned above to secure our phone system. I guess there are scripts that targets all VoIP providers defined networks, on all their IPs, otherwise automated tools wouldn’t have caught our IPs so quickly.
IIRC, there was another setting too that I used, I think it’s “alwaysauthreject=yes” in sip conf, not sure if it was for this purpose or not to be honest, it was a long time ago.
I use 30+ long passwords for every extension, and a firewall on top for anything external and internal.
It’s the same with remote SSH logins, any linux server on a public IP will see automatic login attempts on the root user, that’s why we also disable remote root login on all our public systems.



2 comments
Comments feed for this article
Trackback link: https://www.tolaris.com/2014/05/29/voice-over-ip-fraud-caused-by-insecure-sip-phones/trackback/