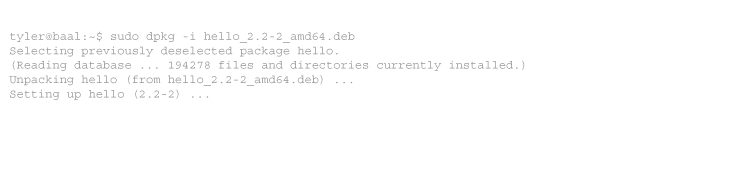
I am about to leave on a business trip, which means I once again have to deal with hotel WiFi. I don’t like WiFi in hotels for two reasons – they almost never provision enough network capacity, and they usually have some kind of irritating captive portal system.
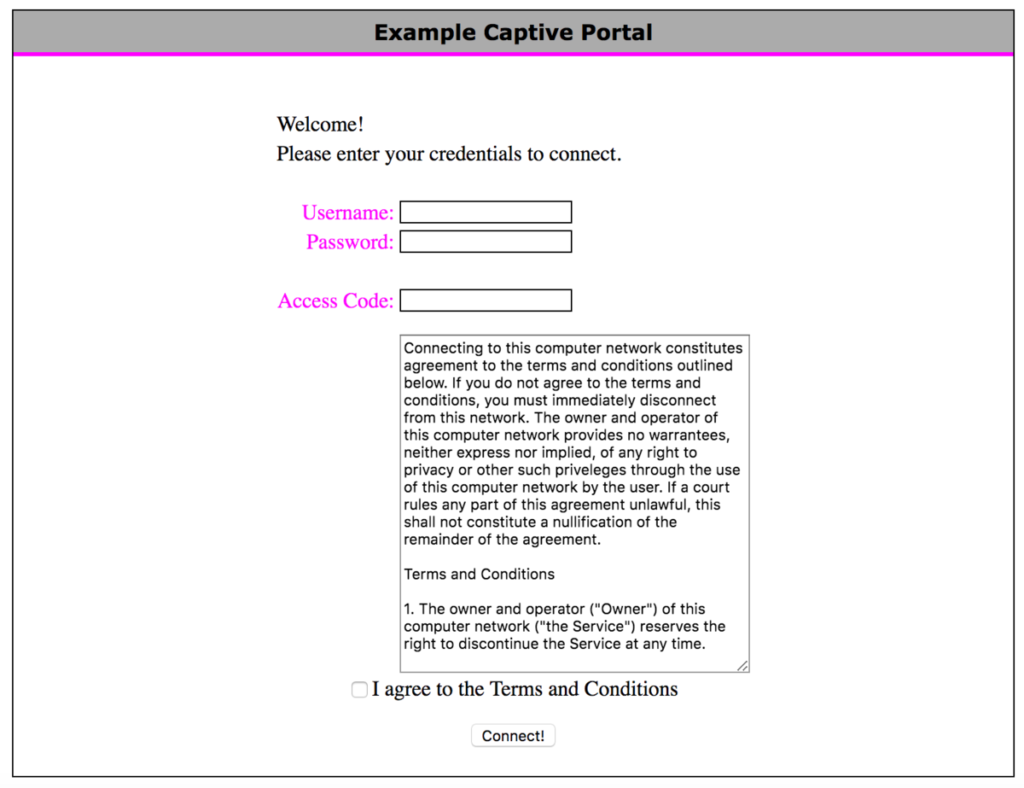
Captive portals often have frustrating limitations, like only allowing a small number of devices on the same login, or regularly requiring those devices to login again to the portal. On top of that, hotel WiFi often uses AP isolation (preventing clients from talking to each other directly) or other issues that make Google Chromecast not work. And finally, configuring all my devices to use the different WiFi settings in each location is tedious.



Recent Comments