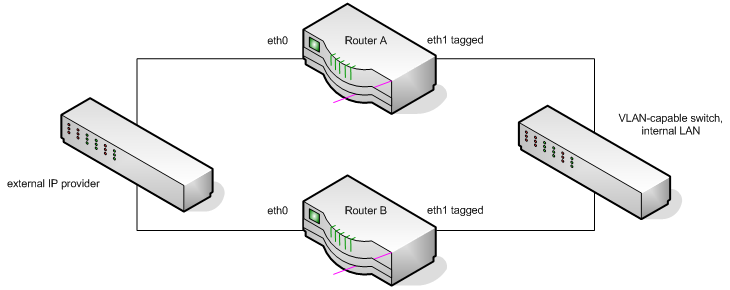
We run several virtual machine host servers on a network with multiple VLANs. The virtual machines are members of different VLANs, but are not themselves aware of the VLAN. This is how we did it.
You are currently browsing articles tagged networking.
Tags: hardy, kvm, networking, ubuntu, virtualbox
In the last 3 weeks our company mail servers have been slammed with a massive increase in spam relay attempts. Logs showed many failures like so.
Jul 12 14:15:26 mailserver.example.com postfix/smtpd[19885]: NOQUEUE: reject: RCPT from 206.12.0.10.in-addr.arpa[10.0.12.206]: 554 5.7.1 <symons@yahoo.co.uk>: Relay access denied; from=<yyjaqveh@lpsb.com> to=<symons@yahoo.co.uk> proto=ESMTP helo=<206.12.0.10.in-addr.arpa>
IP addresses have been obscured to protect the guilty (or ignorant, as this is certainly a botnet). Unfortunately, a large number of the IP addresses in question belonged to my own satellite customers. Mail servers for our other domains were almost entirely unaffected. Which tells me that some bastard has written a botnet spam client that looks up its own public IP, finds the reverse DNS entry, looks up the MX record of the corresponding domain, and then attempts to relay mail through that server. This is particularly mean, as it will encourage your own ISP to shut you down.
Tags: networking, security
After my recent adventure with reverse-path filtering, I didn’t expect to see it again so soon. And then I took another look at a long-standing annoyance in our OpenVPN network.
I set up OpenVPN so our offices and laptops could securely access internal resources. This lets me print documents directly to another office, for instance. Or access web-based applications that we don’t make available to the public. Or remotely SSH into a PC and fix a problem. Read the rest of this entry »
Tags: kernel, networking, openvpn
I recently created a very complex network using routers running Ubuntu Hardy. These routers were configured with the following features:
- failover shared IP addresses using heartbeat
- routing announcements via Quagga BGPd
- 802.1q VLAN tagging
- multiple physical interfaces
During debugging of this network, I encountered an odd scenario whereby traffic coming in from the external interface (eth0) could not reach the IP address of the secondary (inactive) router’s internal interface (eth1, VLAN tagged).
Tags: kernel, networking
Update 2012-05-16: These instructions have been superseded by a new version of this guide. Follow that document instead.
Update 2010-08-18: These instructions are still valid as of VirtualBox 3.2.8 and Ubuntu 10.04 “Lucid Lynx”. VirtualBox now creates a “vboxnet0” interface by default, but this is not a bridge.
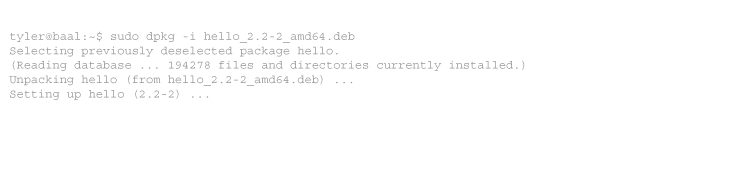
I use VirtualBox every day. The satellite world is infested with bad Windows-based management tools that fail to run in Wine. So I often run those apps in a Windows virtual machine, safely sandboxed the way Windows belongs.
Note to hardware developers: if your network-based device does not have a standards-compliant HTTP interface, you lose. If it has a Windows-based management tool instead, you lose twice. I will buy your product only if I have no other choice.
I imagine running Windows apps is what 90% of VirtualBox users use it for, but it can do so much more than that. I also run several Linux-based VMs, and use them to test server configs, or even whole networks before rolling out the real thing. If you do this, you probably want to use more than the basic NAT networking that VirtualBox uses by default. For instance, wouldn’t it be nice to install an SSH server in the VM, minimise the VirtualBox GUI, and SSH in from a terminal just like you would a real server?
Tags: networking, virtualbox
I frequently travel to the Middle East, which means I often find myself on the wrong end of a slow Internet link. Sometimes that is oversold undersea fibre, such as in Dubai. More often – because of my work – it is VSAT. I’m an engineer, which means I’m a curious monkey that takes everything apart just to understand how it works. Network topology is one of those things.
Tags: fibre, networking, satellite



Recent Comments