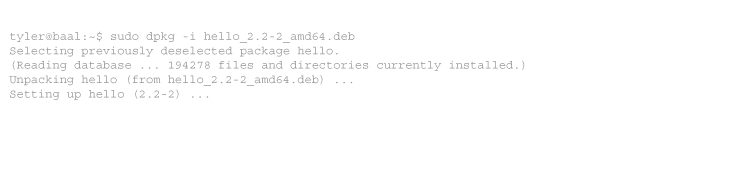
The Wireshark team has long warned us not to run Wireshark as root. However, since Wireshark 1.4 (between Ubuntu 10.04 and 12.04), they’ve raised the stakes. Wireshark no longer loads all its plugins and protocol dissectors when run by root, and it displays warning messages on the CLI and the GUI:
root@laptop:~# tshark tshark: Lua: Error during loading: [string "/usr/share/wireshark/init.lua"]:45: dofile has been disabled Running as user "root" and group "root". This could be dangerous.
Although I’ve long been aware of the dangers of running Wireshark as root, the convenience has outweighed the danger until now. The annoyance of this new output finally prompted me to act. The solution is to use Linux capabilities to allow Wireshark to sniff without using any of root’s other permissions.
There are plenty of instructions out there telling people how to do this. Ubuntu users (since 10.04) have a very easy method. All solutions involve granting the CAP_NET_RAW and CAP_NET_ADMIN capabilities to any binary you want to allow to sniff:
sudo setcap cap_net_raw,cap_net_admin+eip /usr/bin/dumpcap
However, this allows all local users to sniff. On a normal workstation, that’s probably fine. But if you want to be more secure, you can restrict access to /usr/bin/dumpcap to certain groups. “adm” is a good choice for most distributions, as console users are generally members. Alternately, consider the group “sudo” (Ubuntu 12.04 or later), “admin” (Ubuntu before 12.04), or “wheel” (Red Hat systems).
sudo chgrp adm /usr/bin/dumpcap sudo chmod 750 /usr/bin/dumpcap
In addition to wireshark, there are a number of other programs that I like to run as an unprivileged user. For my notes and yours:
for i in `which dumpcap iftop ngrep tcpdump tcptraceroute traceroute.db` ; do sudo setcap cap_net_raw,cap_net_admin+eip $i done
nmap is a special case. More on that later now.
The only problem I’ve found with this method is that unprivileged users still cannot sniff USB packets. For now only root can do that.
Tags: networking, security, wireshark



No comments
Comments feed for this article
Trackback link: https://www.tolaris.com/2013/01/23/sniffing-with-wireshark-as-an-unprivileged-user/trackback/