In the last 3 weeks our company mail servers have been slammed with a massive increase in spam relay attempts. Logs showed many failures like so.
Jul 12 14:15:26 mailserver.example.com postfix/smtpd[19885]: NOQUEUE: reject: RCPT from 206.12.0.10.in-addr.arpa[10.0.12.206]: 554 5.7.1 <symons@yahoo.co.uk>: Relay access denied; from=<yyjaqveh@lpsb.com> to=<symons@yahoo.co.uk> proto=ESMTP helo=<206.12.0.10.in-addr.arpa>
IP addresses have been obscured to protect the guilty (or ignorant, as this is certainly a botnet). Unfortunately, a large number of the IP addresses in question belonged to my own satellite customers. Mail servers for our other domains were almost entirely unaffected. Which tells me that some bastard has written a botnet spam client that looks up its own public IP, finds the reverse DNS entry, looks up the MX record of the corresponding domain, and then attempts to relay mail through that server. This is particularly mean, as it will encourage your own ISP to shut you down.
I ignored these attempts at first. The server was rejecting them and the botnet didn’t appear to be trying to relay through anyone else (according to traffic logs). With our Postfix settings it was unlikely they’d ever succeed. Then the log entries moved from “annoying” to “problematical”:
Jul 13 20:34:50 mailserver.example.com postfix/master[18904]: warning: service “smtp” (25) has reached its process limit “200”: new clients may experience noticeable delays
Jul 13 20:34:50 mailserver.example.com postfix/master[18904]: warning: to avoid this condition, increase the process count in master.cf or reduce the service time per client
Jul 13 20:34:50 mailserver.example.com postfix/master[18904]: warning: see http://www.postfix.org/STRESS_README.html for examples of stress-adapting configuration settings
Time to do something about it. We already use fail2ban to protect other services, so I enabled the postfix rules. In /etc/fail2ban/jail.local:
[postfix] enabled = true ignoreip = 127.0.0.1/8 # suggest listing your valid server IP ranges here port = smtp,ssmtp filter = postfix logpath = /var/log/mail.log bantime = 3600
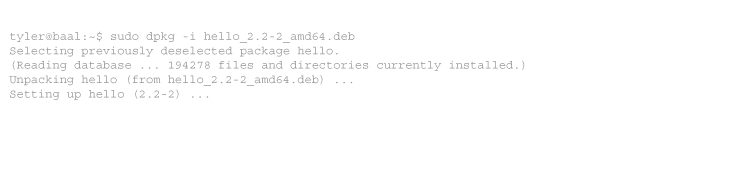
I then reloaded fail2ban, and waited for results. Within a few minutes (fail2ban takes time to parse existing logs), 65 IP addresses were banned. Here are my results 24 hours later, edited for brevity:
root@mailserver:/etc/fail2ban# fail2ban-client status postfix
Status for the jail: postfix |- filter | |- File list: /var/log/mail.log | |- Currently failed: 49 | `- Total failed: 58171 `- action |- Currently banned: 68 | `- IP list: ... `- Total banned: 3883
Now to hunt down the customers with botnet infections and start sending “violation of terms of service” warnings.
Tags: networking, security



1 comment
Comments feed for this article
Trackback link: https://www.tolaris.com/2009/07/15/stopping-spam-botnets-with-fail2ban/trackback/